In this challenge we get a Windows XP memory dump and we are told to get the password inside a KeePassX file.
KeePassX stores critical key encrypted in memory following a memory dump attack described here: http://systemoverlord.com/sites/default/files/projects/KeePassX.pdf
But it’s still possible to dump keys with the current version. Please see Hugo Caron’s draft paper at: http://haxogreen.lu/schedule/2012/attachments/3_CFP_MemoryAnalysis_PasswordManager_slides
(There is 2 small mistakes in this draft paper, follow this write-up and see if you can catch them)
We first dump the process memory and the adressable memory using Volatility:
$ vol.py -f memdump.raw –dump-dir=dump memdump -p 768
Volatile Systems Volatility Framework 1.4_rc1
************************************************************************
Writing KeePassX.exe [ 768] to 768.dmp$ vol.py -f memdump.raw –dump-dir=dump procmemdump -p 768
Volatile Systems Volatility Framework 1.4_rc1
************************************************************************
Dumping KeePassX.exe, pid: 768 output: executable.768.exe
We can load the exe file in IDA.
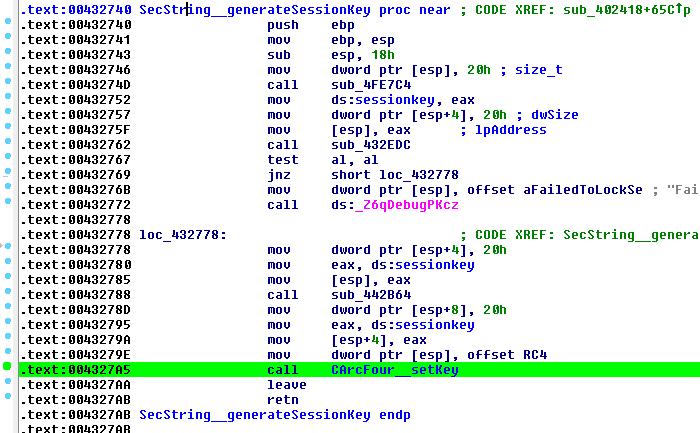
Every critical keys is stored encrypted in a modified RC4 form when not being used. The key for all these containers is the same session key. And this session key is stored in a static variable in the bss so the offset will always be the same for a given exe file.
Here is the code that initialize this session key:
Lets check the memory with IDA (remember we created this exe from the memory dump so the BSS section is already filled)
A nice pointer. Now we use Volatility to dump the memory content at 0xc01b00:
>>> cc(pid=768)
Current context: process KeePassX.exe, pid=768, ppid=1584 DTB=0x2e00240
>>> db(0xc01b00, 32)
00c01b00 db a9 65 b9 73 a4 40 7a 8f 66 06 90 42 7c 29 92 ..e.s.@z.f..B|).
00c01b10 f7 c2 3c 57 7c 9c f1 fc 9d 5d e8 c5 66 7a 71 b3 ..<W|….]..fzq.
Wonderful, the session key is: dba965b973a4407a8f660690427c2992f7c23c577c9cf1fc9d5de8c5667a71b3
Now we need to find in the memory the MasterKey. The MasterKey is the SHA256 hashed password of the kdb file. From the MasterKey, the AES key is derived (SHA) for actual encryption of the kdb file.
Storage of protected strings is done using a structure called SecData:
(...)
private:
quint8* data;
int length;
bool locked;
};
In memory, every SecData object will be stored as:
[int pointer][int length][bool locked]
We are looking for the MasterKey which is 32 bytes long and we know the key is going to be locked. So we are looking for:
[pointer][20000000][01]
The following python script will use heuristic to find pointer candidates and then uses the stolen session key to decrypt it using KeePassX’s modified RC4:
import struct
import binascii
# !!!!! THIS IS A MODIFIED RC4 IMPLEMENTATION TO MATCH KEEPASSX'S
# do the key schedule. return a byte array for the main algorithm
# k can be a list of numbers or a string
def rc4_init(k):
k = binascii.unhexlify(k)
# create and initialise S
s = range(256)
# process S using the key data
j = 0
kl = len(k)
ka = 32 << 1
i = 0
while i < 256:
j = (j + s[i] + ord(k[i % kl]) + 0x40) % 256
s[0], s[j] = s[j], s[0]
i = i + 1
return s
# encrypt/decrypt a string using RC4
def rc4(s, val):
l = len(val)
buf = bytearray(l)
i = 0
j = 0
idx = 0
while idx < l:
i = (i + 1) % 256
j = (j + s[i]) % 256
s[i], s[j] = s[j], s[i]
k = s[(s[i] + s[j]) % 256]
buf[idx] = (ord(val[idx])) ^ k
idx = idx + 1
return str(buf)
memory = open("768.dmp", "rb").read()
p = 0
size_byte = 1
size_int = 4
memory_offset = 10977280
search_length = struct.pack('<L', 32)
search_locked = struct.pack('B', 1)
session_key = "dba965b973a4407a8f660690427c2992f7c23c577c9cf1fc9d5de8c5667a71b3"
while p < len(memory):
cell1 = memory[p:p+size_int]
if cell1 == search_length:
cell2 = memory[p+len(search_length):p+len(search_length)+size_byte]
if cell2 == search_locked:
cell3 = memory[p-size_int:p]
search_data = struct.unpack('<L', cell3)[0]
file_offset = search_data - memory_offset
if (file_offset > 0 and file_offset < len(memory)):
data = memory[file_offset:file_offset+32]
clear = rc4(rc4_init(session_key), data)
print "Found pointer at file offset=", \
hex(p-size_int), "pointer=", \
hex(search_data), \
hex(struct.unpack('<L', cell1)[0]), \
struct.unpack('B', cell2)[0], \
"data offset=", hex(file_offset), "data=", binascii.hexlify(data), \
"clear=", binascii.hexlify(clear)
p += size_int
Lets run it:
Found pointer at file offset= 0x865f0 pointer= 0x1000004 0x20 1 data offset= 0x588004 data= 6a240aff6a240aff6a240aff6a240aff6a240aff6a240aff6a240aff6a240aff clear= 684f9dbc6560b1c649d75f5943a253186dcf8f3c61513a62dd8957642d6c73c6
Found pointer at file offset= 0x90254 pointer= 0xcf4938 0x20 1 data offset= 0x27c938 data= 090006006f010801d883c9000120012000000000000000000000000001000000 clear= 0b6b91436045b338fb709ca628a658c707eb85c30b75309db7ad5d9b46487939
Found pointer at file offset= 0x1df4ec pointer= 0xc8a510 0x20 1 data offset= 0x212510 data= caa734c900fb9474b54ecd58d73a57c031885df771213b84aadc582e92740c24 clear= c8cca38a0fbf2f4d96bd98fefebc0e273663d8347a540b191d7105b5d53c751d
Found pointer at file offset= 0x1df4f8 pointer= 0xc64f08 0x20 1 data offset= 0x1ecf08 data= caa734c900fb9474b54ecd58d73a57c031885df771213b84aadc582e92740c24 clear= c8cca38a0fbf2f4d96bd98fefebc0e273663d8347a540b191d7105b5d53c751d
Found pointer at file offset= 0x1df504 pointer= 0xc82b90 0x20 1 data offset= 0x20ab90 data= 682bc8000100000001000000010000000000000000000000010000001f010000 clear= 6a405f430e44bb3922f355a6288659e707eb85c30b75309db6ad5d9b58497939
Found pointer at file offset= 0x1df510 pointer= 0xc82b68 0x20 1 data offset= 0x20ab68 data= 88afc80005000000050000007a2bc80000005100750069007400740000000000 clear= 8ac45f430a44bb3926f355a653ad91e707ebd4c37e75599dc3ad299b47487939
Found pointer at file offset= 0x1df51c pointer= 0xc8af88 0x20 1 data offset= 0x212f88 data= 8d20fd01ef3da59ba3f0be19d477647148b6e3fea87800130bb145d61aa6f06d clear= 8f4b6a42e0791ea28003ebbffdf13d964f5d663da30d308ebc1c184d5dee8954
Found pointer at file offset= 0x2709f4 pointer= 0xcf4938 0x20 1 data offset= 0x27c938 data= 090006006f010801d883c9000120012000000000000000000000000001000000 clear= 0b6b91436045b338fb709ca628a658c707eb85c30b75309db7ad5d9b46487939
Found pointer at file offset= 0x275094 pointer= 0xcf4938 0x20 1 data offset= 0x27c938 data= 090006006f010801d883c9000120012000000000000000000000000001000000 clear= 0b6b91436045b338fb709ca628a658c707eb85c30b75309db7ad5d9b46487939
Found pointer at file offset= 0x28cf5f4 pointer= 0x2eeb2f8 0x20 1 data offset= 0x24732f8 data= e8ffffff766b00004e00000010733f00010000000000b6bba8ffffff7b003300 clear= ea9468bc792fbb396df355a639f566e706eb85c30b7586261f52a2643c484a39
Found pointer at file offset= 0x28d0840 pointer= 0x2822ea3 0x20 1 data offset= 0x1daaea3 data= 0000000000000000000000000000000000000000000000000000000000000000 clear= 026b97430f44bb3923f355a6298659e707eb85c30b75309db7ad5d9b47487939
Found pointer at file offset= 0x28d5180 pointer= 0x4cc60b4 0x20 1 data offset= 0x424e0b4 data= 0000000000000000000000000000000000000000000000000000000000000000 clear= 026b97430f44bb3923f355a6298659e707eb85c30b75309db7ad5d9b47487939
Found pointer at file offset= 0x440ad54 pointer= 0x100020c 0x20 1 data offset= 0x58820c data= 6a240aff6a240aff6a240aff6a240aff6a240aff6a240aff6a240aff6a240aff clear= 684f9dbc6560b1c649d75f5943a253186dcf8f3c61513a62dd8957642d6c73c6
Obviously some of those are false positives. A good key has a good entropy so we can discard a few keys with many nulls or repeated strings, we are left with:
Found pointer at file offset= 0x1df4f8 pointer= 0xc64f08 0x20 1 data offset= 0x1ecf08 data= caa734c900fb9474b54ecd58d73a57c031885df771213b84aadc582e92740c24 clear= c8cca38a0fbf2f4d96bd98fefebc0e273663d8347a540b191d7105b5d53c751d
Found pointer at file offset= 0x1df51c pointer= 0xc8af88 0x20 1 data offset= 0x212f88 data= 8d20fd01ef3da59ba3f0be19d477647148b6e3fea87800130bb145d61aa6f06d clear= 8f4b6a42e0791ea28003ebbffdf13d964f5d663da30d308ebc1c184d5dee8954
And we have a dupe so we are left with 2 possibles decrypted MasterKey:
c8cca38a0fbf2f4d96bd98fefebc0e273663d8347a540b191d7105b5d53c751d
or
8f4b6a42e0791ea28003ebbffdf13d964f5d663da30d308ebc1c184d5dee8954
Trivial: locate the kdb in the memory dump and save it to a file. Kdb signature is “03d9a29a65fb4bb5”.
Now we have 2 approaches: we can derive the AES key and do manual decryption of the kdb file or we can patch KeePassX to accept a MasterKey instead of a password.
I went with the patched KeePassX because it looked to be easier than do some manual AES processing. (I was wrong of course as it took me some long fiddling to get it working)
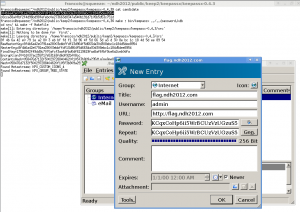
Here is patched KeePassX opening the kdb file after we try 2 candidates MasterKey
Important modifications were:
– Skip raw password transform, we will input a hex string in the password dialog, that hex string is the decrypted MasterKey
Replace
SHA256::hashBuffer(Password_CP1252.data(),*RawMasterKey_CP1252,Password_CP1252.size());
by
convHexToBinaryKey(Password_CP1252.data(),(char*)(*RawMasterKey_CP1252));
– Copy RawMasterKey to MasterKey (RawMasterKey is our decoded hex string)
memcpy(*MasterKey, *RawMasterKey, 32);
Dirty KeePassX patch here (CTF quality)